The storage and secure management of data and passwords is one of the most important aspects in the crypto and blockchain world, and more generally in all online environments.
Encryption, intense as the art of “hidden writings” capable of converting plain text into encrypted text and vice versa, comes to our aid making it difficult for hackers to allow unauthorized access to certain networks and transactions.
Let’s delve into the different methods through which encryption can protect valuable information and safeguard passwords.
Symmetric and asymmetric password encryption in the crypto sector
Generally when talking about password protection in cryptography, reference is made to two encryption methods: symmetric and asymmetric.
That symmetric one refers to a type of text encryption that uses a single key to encrypt and decrypt information:
The encryption key is shared between sender and recipient and is usually agreed upon in advance: it represents the central element that in cryptocurrencies allows users to access and manage their digital resources.
Symmetric encryption with a single key is one of the most common means to protect passwords, transactions, and communication between operating nodes.
When performing, for example, a funds transfer from one wallet to another, it ensures that the information is read and shared only by two parties involved in the transaction, keeping the data safe from prying eyes.
However, despite the advantages it brings, symmetric encryption has limitations in terms of scalability and key management.
Indeed, the need for communication in pairs greatly limits the expansion of this practice in a system with many more users. At the same time, more users imply human errors in the management and conservation of the so-called “private key”, which if lost leads to the loss of crypto or data stored in the virtual wallet.
To overcome these limitations, asymmetric cryptography comes to our aid by providing a pair of separate keys (public and private) in the encoding and decoding of passwords.
This additional level of security instantly increases data protection: the public key can be shared with anyone on any network (like when we share our address to receive a payment in crypto), while the private key must be kept secret.
Both keys are generated by an algorithm that uses large prime numbers to create two unique and mathematically linked keys.
Anyway, whoever possesses the public key can encrypt a message, but only the holder of the private counterpart can decrypt the text. We can imagine this as if it were an email inbox: whoever holds the public key can send a message, but only the owner of the private key can open the email and read the messages.
Non-custodial software wallets like Trust Wallet or MetaMask use asymmetric cryptography to offer the highest possible security to their users.
Source: https://www.javaboss.it/crittografia-in-java/
The most common formats of encrypted passwords
Password encryption in the crypto and blockchain sector occurs according to different formats that can be used for different purposes and offer different levels of security:
- MD5 (Message Digest 5):
The MD5 algorithm, developed by Ronald Rivest in 1991, generates a 128-bit hash (32 hexadecimal characters) from a variable-length input.
It is no longer considered secure due to vulnerabilities discovered in its algorithm. However, it is still used in some legacy contexts, for example to verify the integrity of files.
- SHA-1 (Secure Hash Algorithm 1):
SHA-1 generates a 160-bit hash (40 hexadecimal characters).
It is no longer considered as secure as it once was, having shown several vulnerabilities: it is now generally replaced by more robust algorithms such as SHA-256 and SHA-3. However, it is still used in a wide range of systems and new applications.
- Salt:
The salt is a random sequence of bits that is added to the password before calculating the hash.
It solves the problem of collisions (two different passwords generating the same hash) in hashing methods.
By adding a salt, even identical passwords will have completely different hashes. This makes it harder for attackers to decrypt passwords through brute force attacks.
- Bcrypt:
Bcrypt is a hashing algorithm specifically designed for password encryption.
Use a salt and a number of iterations to slow down the hash calculation. It is widely used to protect user passwords in the field of databases.
The choice of encryption format depends on the specific needs of the reference system. Nowadays, it is advisable to use hashing algorithms such as bcrypt or SHA-2 to protect passwords and mitigate cyber attacks.
Hash functions and digital signatures
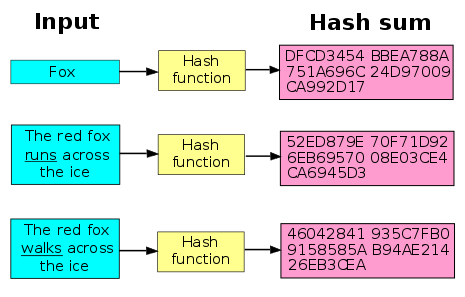
Another way to protect passwords and valuable information in cryptocurrencies is to rely on hash functions, that is algorithms that transform any form of data into a string of characters of fixed length.
By using robust hashing algorithms, we can effectively protect sensitive information and prevent cyber attacks.
Hash functions are irreversible: it is not possible to convert a hash back into its original data. They are essential in data management on the blockchain because they allow structuring information without compromising its initial integrity
Hashes can also act as fingerprints for all encrypted passwords, protecting the user against unauthorized actions on their account.
Indeed, any modification to the original data would result in a new hash, which would no longer correspond to the original source and therefore would not be verifiable on the blockchain.
Another method to ensure password security, and more specifically the authenticity and integrity of data in a message, is to use the so-called “digital signatures” (asymmetric cryptography technique).
This is simply a method to ensure that the owner of those specific data is approving the transaction. Generally, the sender creates the digital signature using a private key to encrypt the signature data, while the recipient obtains the signer’s public key to decrypt the data. This code represents irrefutable proof that a message has been created solely by the sender and has not been tampered with online.
When talking about digital signatures, one immediately thinks of signature devices like Ledger, Trezor, and Bitbox that allow to validate a transaction before it is broadcasted to the rest of a cryptographic network.
However, be careful not to consider these devices as wallets: they do not contain your cryptocurrencies but only allow you to approve the transactions necessary to spend them.
We often say, “my crypto is ON my Ledger”.
But your digital assets aren’t actually stored physically on your Ledger – they’re on the blockchain.
Your Ledger stores and protects your private keys and keeps them safe so you can fully own and manage your assets.@iancr explains: pic.twitter.com/PGrmQIvKpV
— Ledger (@Ledger) May 11, 2023

